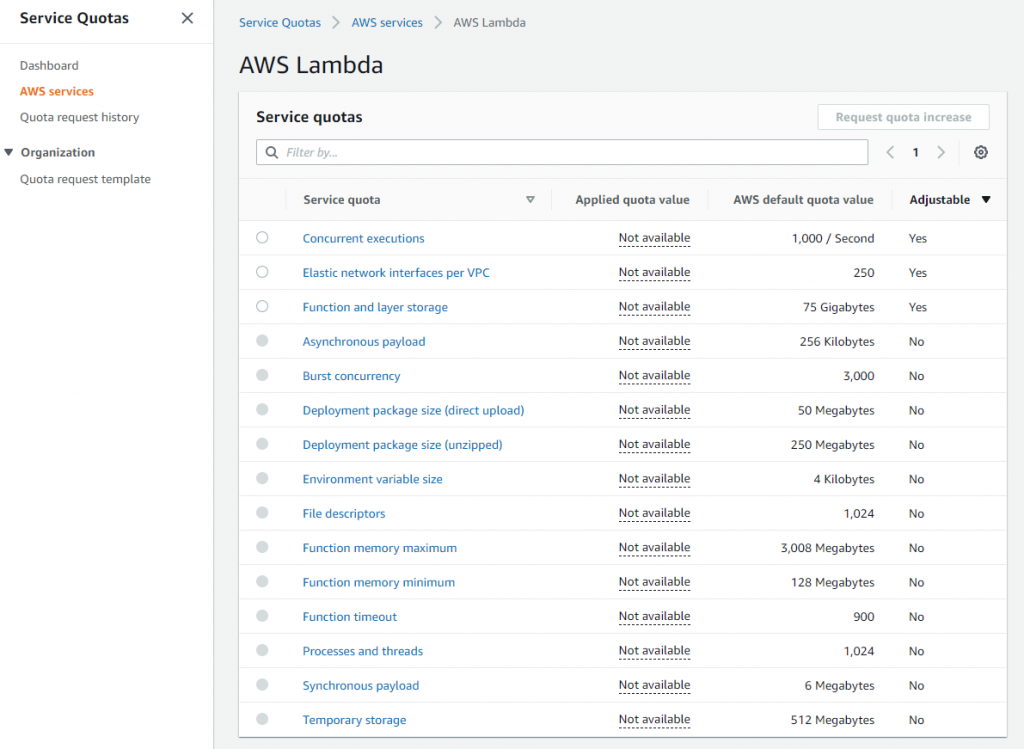
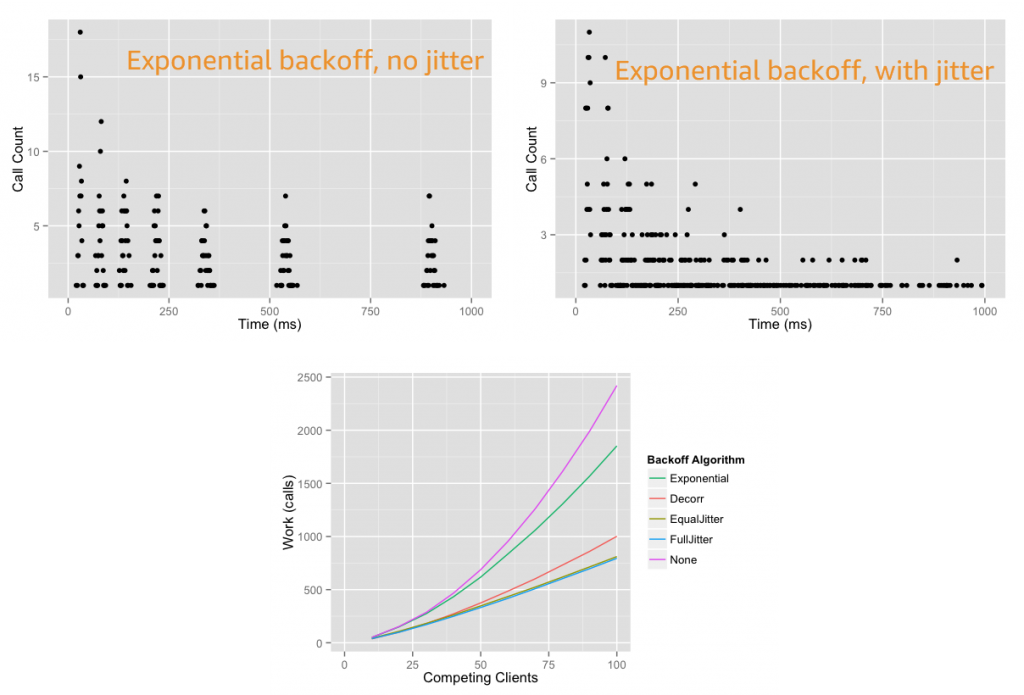
Building well-architected serverless applications: Building in resiliency – part 2
This series of blog posts uses the AWS Well-Architected Tool with the Serverless Lens to help customers build and operate applications using best practices. In each post, I address the serverless-specific questions identified by the Serverless
Building well-architected serverless applications: Building in resiliency – part 1
This series of blog posts uses the AWS Well-Architected Tool with the Serverless Lens to help customers build and operate applications using best practices. In each post, I address the serverless-specific questions identified by the Serverless
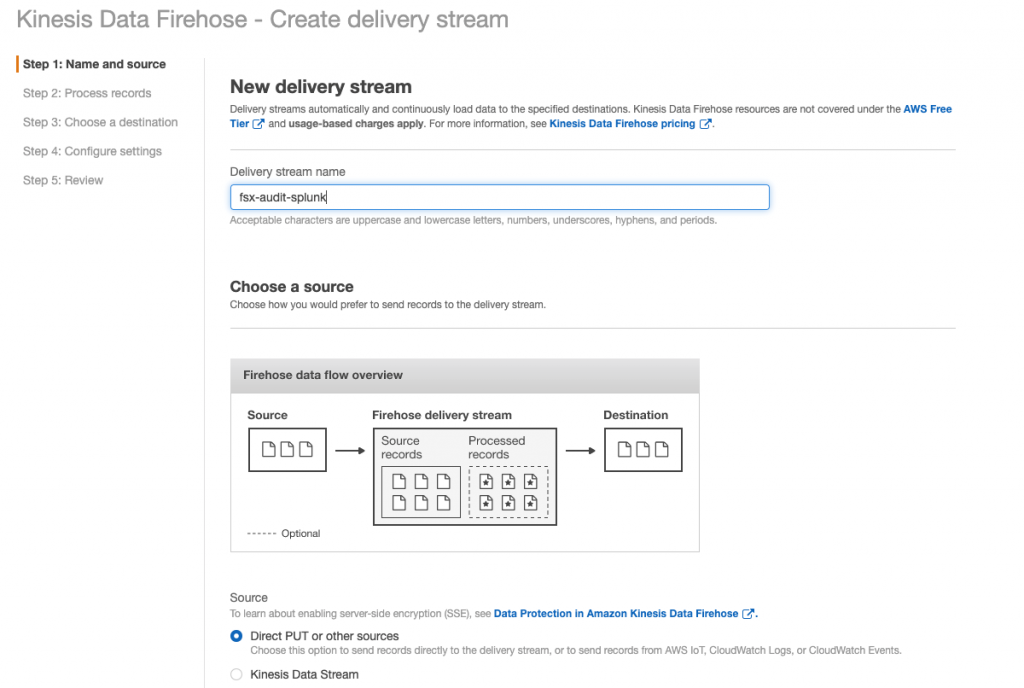
Monitoring and reporting Amazon FSx user access events using Splunk
Monitoring end-user activity and access to data is core to any modern data security strategy. As customers migrate workloads to the cloud, logging end-user accesses of customer data is a key component of internal security policies and is required to
Accessing CloudEndure Disaster Recovery with Okta single sign-on
Many organizations use single sign-on (SSO) to ensure security and compliance, streamline access management, and improve their user experience. Some organizations require all corporate applications, workloads, and solutions to use SSO for authentication, including their disaster recovery (DR) solution.